Force Login Everytime in Spring Boot Secirity Updated FREE
Force Login Everytime in Spring Boot Secirity
In this post, we will await at the spring security login example. Login is role of the Spring Security authentication procedure. We already covered the Spring Security Hallmark Providers which is core to the spring security login procedure.
Introduction
For most of the spider web application, the common style of authentication works where user provides the username and countersign and system validate the credentials to make sure they are valid. Bound security supports the following mode for the login process.
- Class login (custom fill the username and password)
- Basic authentication.
- Digest
When we provide the credentials, spring has multiple ways to read the details for the authentication, which includes.
- In Retentivity Storage (Not useful in the real-globe applications)
- JDBC Authentication.
- Custom User Details Service (We will use this approach)
- LDAP (More often than not for Intranet applications)
Before we move with the code, information technology'southward very important that nosotros have the clarity of the login workflow.
ane. Spring Security Login
Let'south look at the login workflow:
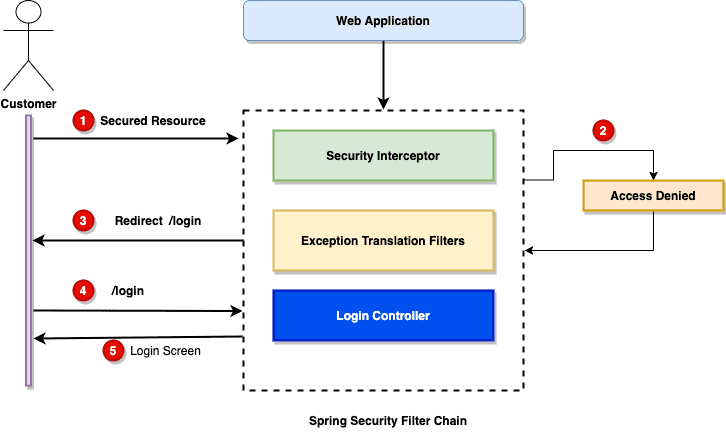
Let's have a quick expect at the workflow:
- User trying to admission secured resources (We allow access to log in user).
- The Spring security filter chain volition throw exception, showing that it does not permit the access to the unauthenticated user.
- The
ExceptionTranslationFilterstarts Start<em>Authentication</em>and send the client to the login page. - Browser request for the login page.
- It shows the login screen to the customer.
Now we empathise the workflow, allow's build our application to let customer login.
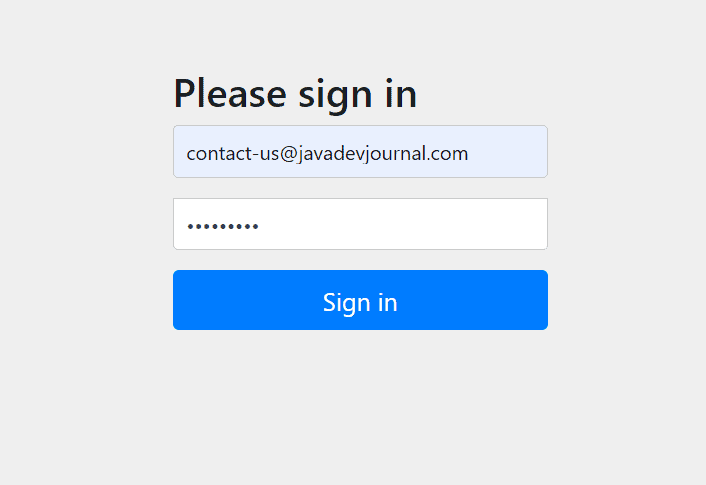
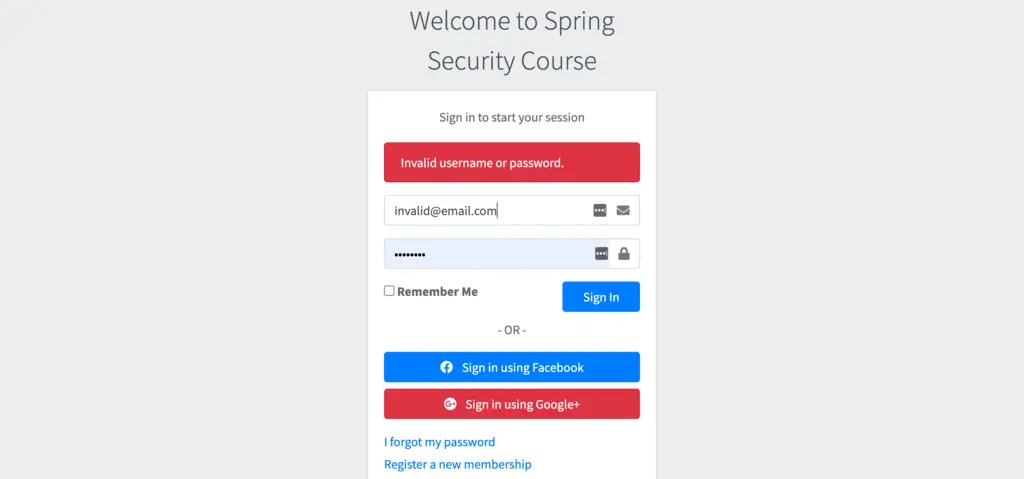
2. Default Security Login Page
By default, Spring security will show the default login page. If you don't practice any customization or configuration, you might see a like login page on your application.
Most application volition similar to have their own customize login page . Spring security provides a flexible option to configure custom login folio for our application. The next section will cover the customization and configuration of the login page.
3. Security Security Custom Login Folio
To enable the custom login folio , override the configure(HttpSecurity http) method by extending the WebSecurityConfigurerAdapter class. Let's wait at the configuration:
@Override protected void configure(HttpSecurity http) throws Exception { http.authorizeRequests() .formLogin(course - > form .loginPage("/login") .defaultSuccessUrl("/dwelling") .failureUrl("/login?mistake=true") ); } Setting up few things in above lawmaking:
- We are configuring the login page URL as
/login, this tells spring security to telephone call this URL earlier displaying the login page. - Nosotros need to create a controller mapped to the "
/login" get asking. Our controller is now responsible to return the login page HTML. - On the successful login, we are redirecting the user to the
/homeURL. This will display the home page to the client. - For failed login endeavor, we proceed user on the same URL but add together a param as "fault=true".
In the afterwards function of this series, nosotros will also configure the success and failure handlers. Handlers are a smashing way to mail processing.
3.ane. Login Controller
With the in a higher place configuration, we also need the login controller to maps GET /login to our controller. Our controller volition return the custom login page. Here is the login page controller for your reference:
package com.javadevjournal.web.controller; import org.springframework.stereotype.Controller; import org.springframework.web.demark.annotation.GetMapping; @Controller public form LoginPageController { @GetMapping("/login") public String login(){ return "account/login"; } } In that location is cypher special about the leap security login controller .
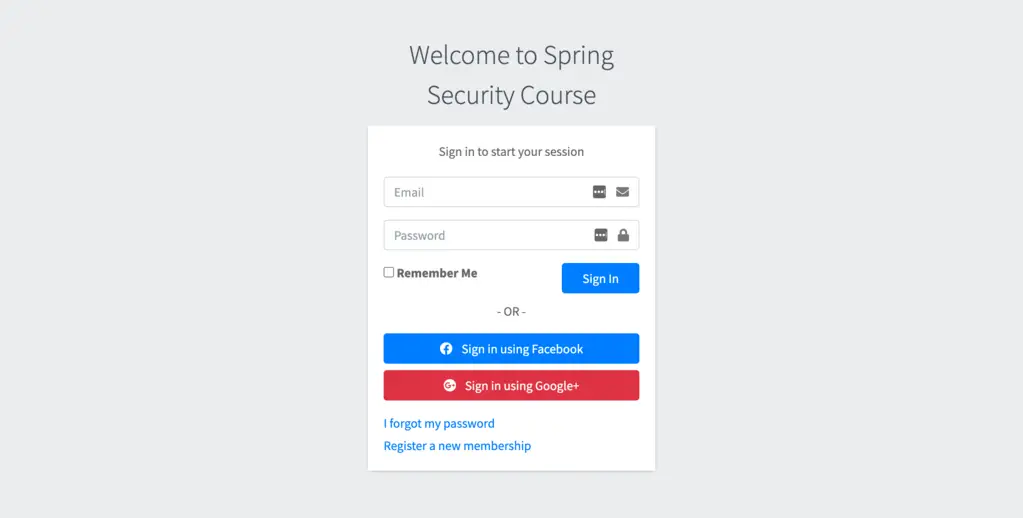
3.two. Login Page
Nosotros need to create a login page as per our design. Our controller will render this folio. I am using Thymeleaf to build the folio, only you can use any other templating engine of your choice.
<!DOCTYPE html> <html xmlns:th="http://world wide web.thymeleaf.org" lang="en"> <head th:replace="core/header :: head"> <meta charset="utf-8"> </head> <torso class="hold-transition login-page"> <div grade="login-box"> <div class="login-logo"> <div class="card"> <div class="card-body login-card-trunk"> <p class="login-box-msg">Sign in to start your session</p> <p th:if="${loginError}" class="mistake">Wrong user or password</p> <form th:activity="@{/login}" method="postal service"> <div th:if="${param.fault}"> <div class="warning alert-danger"> Invalid username or password. </div> </div> <div class="input-grouping mb-3"> <input blazon="email" class="form-control" name="username" placeholder="Email"> <div class="input-group-append"> <div class="input-group-text"> <span grade="fas fa-envelope"></span> </div> </div> </div> <div class="input-group mb-3"> <input type="countersign" name="password" class="grade-control" placeholder="Countersign"> <div form="input-grouping-append"> <div grade="input-group-text"> <span class="fas fa-lock"></span> </div> </div> </div> <div grade="row"> <div class="col-4"> <button type="submit" class="btn btn-principal btn-block">Sign In</push> </div> <!-- /.col --> </div> </course> </body> </html> It's a simple HTML page, but let's highlight a few of import points in the HTML.
- Our grade will perform a mail service request to
/login. - The
/loginhandled automatically by Spring security. We need non create whatever controller method for the mail service request. - From field parameters should be
usernameandpassword(brand certain they take exactly same name equally the/loginmapping expecting these parameters). - For the failed login endeavour, it sends back an HTTP parameter. Nosotros are using the parameter to display the error message to the customer (check
param.errorin the HTML).
Spring security will automatically include CSRF token as a hidden field. This is a security feature. We volition talk over it in the later section of this course.
4. Spring Security Login Configurations
Nosotros have completed the custom login page for the leap security , basic configurations are too in place. For the Spring Boot application, spring security will exist agile by calculation the spring security stater in the classpath. Information technology volition start prompting for username and countersign.
To enable the Bound Security's web security support and provide the Spring MVC integration, nosotros will add the @EnableWebSecurity to our security configuration course.We also need some additional steps for the security configuration.
- We desire to permit certain pages to be accessible without forcing the user to login.
- Certain part of the application should be secure and we will force the customer to login.
- Nosotros like the CSS and other static content outside of the security (until yous desire to secure them)
Here is our security configuration class:
@EnableWebSecurity public class AppSecurityConfig extends WebSecurityConfigurerAdapter { @Override protected void configure(HttpSecurity http) throws Exception { http.authorizeRequests() .antMatchers("/login", "/annals") .permitAll() .antMatchers("/account/**").admission("hasRole('ROLE_ADMIN')") .and() .formLogin(class - > form .loginPage("/login") .defaultSuccessUrl("/home") .failureUrl("/login?error=true") ); } @Override public void configure(WebSecurity web) { web.ignoring() .antMatchers("/resources/**", "/static/**"); } } Hither are some important points to consider:
- Login and annals page to exist accessible without any login. Permitting it to all users using the
antMatchersdesign. - We are assuasive only logged is customer to access URLs matching with pattern
/business relationship/**. Looking for a certain role before allowing the user to access the URL. - WebSecurityConfigurerAdapter provides a set up of methods to enable specific web security configuration.
-
@EnableWebSecurityenable jump security supports with support for the Jump MVC integration. -
configure(HttpSecurity http)method is used to configure distinct security points for our awarding (e.g. secure and non-secure urls, success handlers etc.).
4.one. Landing Page for Successful Authentication
After the successful authentication, we want to redirect customer to the abode screen. Spring security provide flexible style to exercise this.
http.authorizeRequests() .... .formLogin(form - > form .defaultSuccessUrl("/dwelling") ); iv.2. Landing Page Failure
If we like, we can redirect the user to unlike URL in example of authentication failure. This can be easily done using the security configuration.
http.authorizeRequests() .... .formLogin(form - > class .failureUrl("/login?fault=true") ); 5. Configuring the Security Authentication Provider
The last part of the application is to configure the authentication provider. Nosotros will inject the custom UserDetailService in the authentication provider .
@Bean public DaoAuthenticationProvider authProvider() { DaoAuthenticationProvider authProvider = new DaoAuthenticationProvider(); authProvider.setUserDetailsService(userDetailsService); authProvider.setPasswordEncoder(passwordEncoder); render authProvider; } @Override protected void configure(AuthenticationManagerBuilder auth) { auth.authenticationProvider(authProvider()); } For more than details, read jump security hallmark provider (I assume that yous are following the complete series). Before we start the login process, make sure you take followed the spring security business relationship registration procedure.
6. Leap Security Custom UserDetailService
If y'all look closely, we are injecting custom UserDetailService in the DAOAuthenticationProvider. This UserDetailsService class will help us with post-obit tasks.
- Try to find the customer in the database based on our information model (Remember Spring security needs to load customer information earlier hallmark).
- Provide data about the user government.
- Authorities helps spring security to decide if a customer can access a resource or not.
@Service public class CustomUserDetailService implements UserDetailsService { @Autowired UserRepository userRepository; @Override public UserDetails loadUserByUsername(String email) throws UsernameNotFoundException { terminal UserEntity customer = userRepository.findByEmail(e-mail); if (customer == null) { throw new UsernameNotFoundException(email); } UserDetails user = User.withUsername(customer.getEmail()) .password(client.getPassword()) .authorities("USER").build(); return user; } } We are setting the valid user authorisation as "USER". This volition help the security permit access to URL's with pattern /account/**.
We will larn more than about the roles, authorities and how to use them during this course.
seven. Test Login Process
It'south time to test the login process. Build and run the awarding. Once the application commencement, we will run the following test cases.
- Directly access secure URL (e.g. whatsoever URL with pattern
/account/**), Spring security will force the login by redirecting us to /login page. - Acess the non-secure URL. We should be able to access those with no issue.
- try login with a valid and invalid credentials.
Let's wait at each test case:
7.1. Login With Valid Credential
In one case application upward, open the http://localhost:8080/login URL in your browser. Nosotros volition have the custom login page from spring security.
Provide the valid credentials (which you used while registration), click on the " Sign In " button. Spring security will validate the credentials and will redirect u.s.a. based on our configuration (.defaultSuccessUrl("/home")).
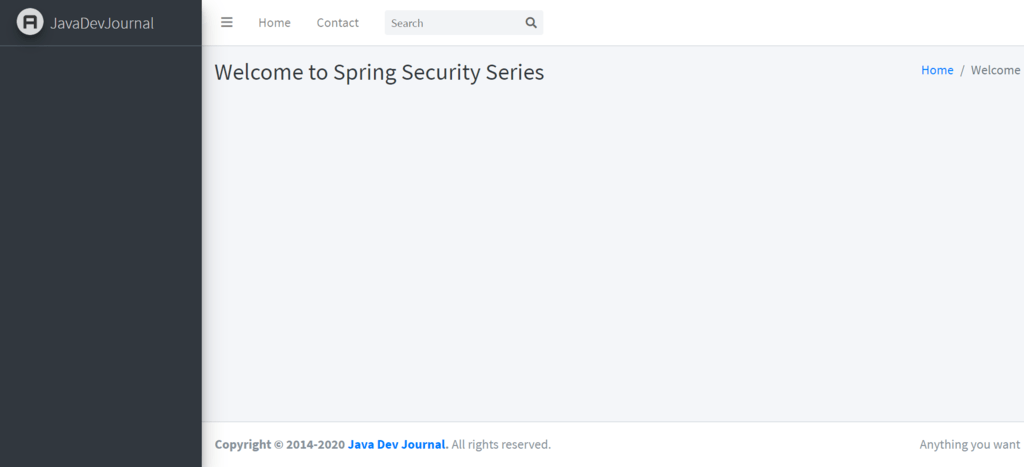
If you lot provide an invalid credential, we volition get the login screen with the error bulletin.
Too, effort to admission the following
http://localhost:8080/account/starter, security configuration will redirect you to the login page. Remember, we have the post-obit in our security configurationantMatchers("/account/**").access("hasRole('ROLE_USER')")
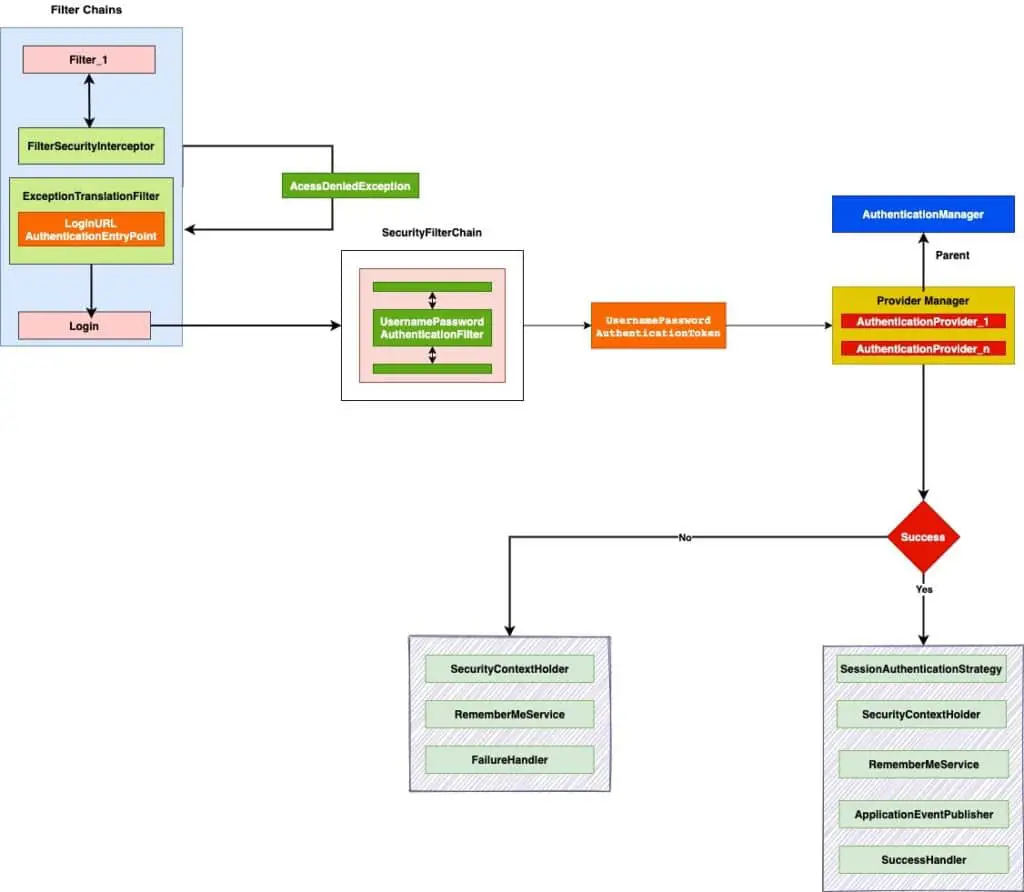
8. Spring Security Login Workflow
We will enhance our login process in this series (Will add together remember me service etc.) but I like to revisit the login workflow
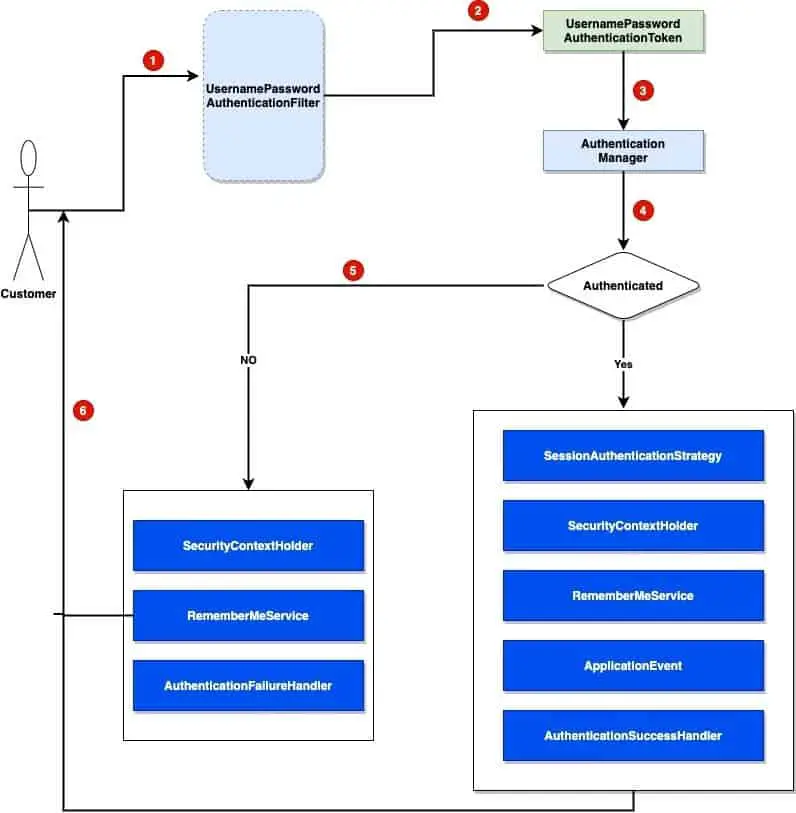
Let's talk about the to a higher place workflow:
- Customer fills out the credentials on the login folio.
- On course submission, the
UsernamePasswordAuthenticationFiltercreates aUsernamePasswordAuthenticationTokenpast extracting the username and password from the request parameters. - The
AuthenticationManageris responsible to validate the user based on the supplied credentials (Look in to theUserUserDetailServiceto sympathize how it works). - If authenticated, Spring security performs several additional operations.
-
SessionAuthenticationStrategyis notified for new login. This handles the HTTP session and makes sure a valid session exists and handles any against session-fixation attacks. - Spring security store the user authentication details in the
SecurityContextHolder. It volition update the SecurityContextHolder with hallmark details. - If
RememberMeServicesservice is active, it will activate theloginSuccessmethod. This service is useful if you want to recall user for sometime (retrieve, on many sites, we accept the option "Keep me Logged in". We can create a similar feature using this service). - It will publish an
InteractiveAuthenticationSuccessEven. - The
AuthenticationSuccessHandleris invoked. This success handler will attempt to redirect the user to the location when we redirect to the login page (due east.g. If you were moving to my business relationship and got the login page, on successful login, it will redirect you to the account page.)
-
- For the neglect effort, Spring security volition also perform a few important steps to make sure it clears out all sensitive and secure data.
- I will articulate the
SecurityContextHolderout. - Call the
loginFailmethod of theRememberMeServicesservice to remove cookies and other related data. - The
AuthenticationFailureHandlertriggers to perform any additional clean-upward action.
- I will articulate the
Here is another overview of the form based login process.
9. Spring Security Success Handler
The Jump Security Success Handlers are a powerful mechanism and strategy to handle a successful user authentication. With .defaultSuccessUrl("/home"), we can redirect the user to a pre-divers location, yet, for enterprise application, we may similar to execute certain operations before redirecting user. Let's think near an eCommerce application, we may like to do following operations after authentication and before user landing on a sure page.
- Nosotros may like to set user default currency and other details in session.
- Like to restore the customer shopping cart.
- Like to redirect the user to sure workflow based on the profile.
The security success handlers are a nifty mode to handle all these business workflows. Spring security provides few success handlers used automatically during the login process.
-
SavedRequestAwareAuthenticationSuccessHandler. -
SimpleUrlAuthenticationSuccessHandler
On successful authentication, Spring security automatically invoke AuthenticationSuccessHandler and it will make certain that customer is redirected to the requested folio when we redirect the customer to the login page. To create custom security handler, we have the following 2 options:
- Create success handler by implementing the
AuthenticationSuccessHandlerinterface. - Extend the sucess handler available with Spring security like
SimpleUrlAuthenitcaionSuccessHandler.
Summary
In this commodity, we discuss the spring security login , we discuss the distinct feature of the login process. To summarize nosotros hash out following points in this post.
- How Jump security login process works?
- Configure and apply custom login page in leap security.
- How to configure the success and failure procedure for our application?
- In the last section, we covered the spring security login workflow.
The source lawmaking for this article is bachelor on the GitHub.
Force Login Everytime in Spring Boot Secirity
DOWNLOAD HERE
Source: https://www.javadevjournal.com/spring-security/spring-security-login/
Posted by: drakegroply.blogspot.com
Comments
Post a Comment